pcNetworking
The User's Information
Security Source
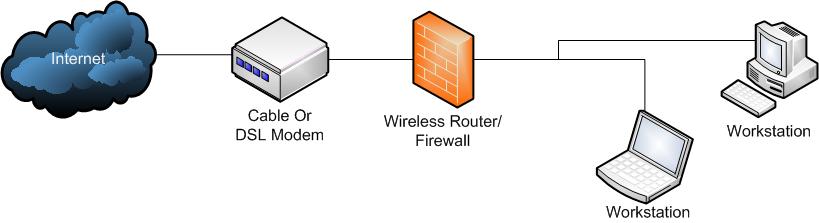
Layers of SecurityIn designing your security strategy you need to look at security from a layered point of view. Each layer in your security reduces the risk to your network and decreases the likelihood of a security breach. Well look at this topic from the outside, meaning the Internet, and step our inward toward your workstations and their own security needs. The InternetThe Internet is the source of most security threats to your environment, but certainly not the exclusive source of threats. Mobile media, external hard drives, internal systems, and portable data device can bring in threats with them in the form of viruses, Trojan horses, and malware can all be introduced through these devices but we'll discuss this more below. The Internet is one of mans greatest accomplishments, and like most technologies, there are those who would use great creations for nefarious purposes. Make no mistake, there are hackers on the Internet who love to get into your network and see what they can find. Whether to exploit your system to launch attacks on other systems of to steal information off of your network, these people do exist and will exploit your environment if given the chance opportunity to do so. As well, the Internet contains many bad downloads and links that will try and drive your system to something they want to exploit. However, using a layered approach we can put up significant resistance to exploitation and save ourselves from most threats. While it would be nice to say that using the techniques on this site would guarantee you will never have an issue, there just no way anyone, or any product can make this claim. Why, because of what we don't know. What is meant by this is that we like to think that our operating system is secure, but we often hear through the media that someone has found a way in to exploit one operating system or another, and this could equally apply to our routers code, or even an exploited portable device we connect to our network. However, there are best practices we will discuss hear to dramatically decrease the likelihood of an attack. After all, which house would one consider more likely to be robbed, the house with the lights out for days with papers piled in the yard showing no signs of life, of the house with the two Rottweilers and the NRA sticker in the back of the truck next to the gun rack. Thus we would submit that by creating layers of security to frustrate possible exploits one would convince an attacker to move on to an easier target, and there are plenty of those online. Router FirewallsOur first line of defense begins with our router which is the device we connect to the Cable or DSL modem coming into the network. These devices have two types of interfaces, the internal interface which is what is connected to the modem, and the internal interface which is usually around four plugs for ethernet cables. As well, if the device also provides wireless connections, these would be considered internal interfaces as well. While it is not practical in this article to explain how to configure the firewall for every possible device users may own (this information will be available in an upcoming additional site feature) we can state that within your users manual and router you will find a setting to enable the firewall as well as configuring rules you may require to support you network. By enabling the router firewall you will take a big step toward preventing unauthorized access to your network through your ISP connection. In general, your network would then look something like this:
As you can see from the diagram above, the firewall stands between your workstations and the Internet. System (Internal) FirewallsSome users may desire to have more granular control over their firewall security and this can be added to your network with the addition of an additional firewall. Why might one want to do this? There could be a number of reasons for example logging? Most "real" firewall provide logging capabilities to show what is going on with traffic on the network. Logs can help you identify things you might not otherwise see or know such as a specific IP address that keeps trying to penetrate the network that could be blocked entirely. The nice thing about this option as well is that there are a number of free firewalls such as Smoothwall that are robust open source firewalls that can run on a rather meager obsolete system you may have laying around to provide not only insight into your network traffic but also allow you to learn a gain a much better level of firewall knowledge you might not otherwise be able to achieve. Another valuable feature of this type of device is that you can also limit system access based upon your own needs. For example, if one has children and do not want them on the Internet from say 10:00pm to 8:00a, with a firewall such as Smoothwall one could add restrictions to control this access. As well, by setting up such a device one could place it between the workstations and the router/firewall above or place it between the cable/DSL modem and the router/firewall depending on ones needs. Granted, as router/firewall become more sophisticated many of these features are starting to surface in these devices, but a standalone firewall usually provides a much better user experience and manageability over the router/firewall alone. PasswordsPasswords your key to the castle. We can't emphasize enough how important good passwords are to securing your system. It boggles the mind that there are people who believe that password as a password would never be guessed by someone looking to penetrate ones network. In fact, password is the #2 most popular password people use. Really?!? So that you are aware, here are the 13 most common passwords used by people and you can find this information in numerous places on the Internet:
Do any of these look familiar to you? If so, you may want to read on. To help you with some considerations of passwords here's a few things to remember:
Why, because of what as known as a brute force password cracking tool. We've tested these tools on passwords on a test system that would allow unlimited tried and noticed the following type of results:
Of course, on a system that disables an account after too many bad tries these tools can be virtually worthless and why one should not only enable these features of their systems but also why one should implement a password expiration policy requiring passwords to be periodically changed. Basic principles of a strong password suggest the following:
Anti VirusAs long as there have been DOS and Windows based machines there have been computer viruses. While we're not trying to pick on Microsoft systems here the simple fact is that their operating systems are the most prolific in the world of computing and hence provide the greatest number of targets. As well, Microsoft has not always done such a great job of closing exploits in operating systems (OS) before releasing them to market. While we applaud all operating systems developers for providing patches once exploits are discovered, the simple fact is that modern operating system contain millions of lines of code, developed by hundreds of developers, and that presents a tough job for OS developers to manage. With such a wide variety of anti virus solutions available today we can only state that you need one or you will at some point have a virus infection that may compromise your system or your data. While one can easily format a hard drive and reinstall the OS and all of the software, if you didn't backup your important data, it will be gone forever and you will have nobody to blame. We will cover anti virus software in our Software Roundup section of the site. Anti MalwareLike viruses, malware presents the same types of threats as viruses albeit in many cases can create additional risks. Malware exists today that can turn your system into a hackers drone allowing your system to mount attacks on other system. While they have control of your system they also have control of your data. Malware can inject Trojan Horse code into your system causing data and performance loss and many other strange unexplainable things to occur. Fortunately, most anti virus solutions also provide anti malware and they too will be covered in the Software Roundup section of the site. Spam FiltersWe've included spam filtering in this discussion for a couple of reasons. First, spam is a big problem today with no real end in site. It's annoying and wastes our time weeding through spam to get to the email we really like to see. However, the greater risk of spam is phishing and the introduction of viruses and malware into the system. Phishing is an email that purports to be from a genuine source such as your bank asking you to send them information such as your login, password, Social Security number, account numbers, and other personal data that can lead to identity theft and other grief. We can categorically say that a reputable organization would NEVER send you an email like this and you should delete it or report it to the organization that the email claims to be from. But if you ever think one is legitimate, give the organization a call to confirm this. Never, under any circumstances send your login, password, Social Security number, account numbers to someone in an email as email is not secure. If you need to share this information call the organization in question or use their website with https at the beginning of the web address to ensure that the information will be sent in a secure fashion. We will also cover spam filters in the Software Roundup section of the site as most security suites today provide this functionality as well. EncryptionEncryption would be the last layer of our multi tiered security discussion, and what we are referring to hear is full disc encryption. Encryption is a technology that takes the data files on your system and garbles them so that they are unusable to those without the correct access to the system. You might ask, "why would I need that"? Consider the following statistics from 2010:
While these statistics apply to laptops which are becoming more people primary workstations, the same risks of data loss and loss of personal information could apply to a stolen desktop as well. With an encrypted system you may not ever get your computer back, as the statistics above would reveal, but at least you wouldn't have to worry about the thief reading through your most personal information and exploiting it against you. We cover encryption in our Software Roundup section of the site as well. In SummarySecuring your network is best done by addressing threats individually to provide the most comprehensive security for your small network. Costs effective tools and software, including some that are free exist today to protect your important information and identity. Becoming familiar with and using these technologies will provide you with a tiered defense that will convince the great majority of bad guys to move on to an easier target and leave your systems alone. As we've mentioned before, there is no such thing as a perfect security system, but most of us don't present the kind of lucrative target that a bad guy would be interested in the first place so the above multi-tiered approach can provide you the peace of mind that you've taken the appropriate steps to point the bad guys elsewhere. | |||||||
|
Copyright (c) 1997 - 2011 - All Right Reserved - pcNetworking.com